Security Awareness & Social Engineering
In network security, structure wins over improvisation: clear paths, fewer privileges and explicit trust boundaries. For **Security Awareness & Social...
22 paginas
In network security, structure wins over improvisation: clear paths, fewer privileges and explicit trust boundaries. For **Security Awareness & Social...
Attack paths shrink as soon as permissions, segments and management channels are consistently configured. For **Wireless & Physical Security** the basis remains the same:...
In network security, structure wins over improvisation: clear paths, fewer privileges and explicit trust boundaries. In **Zero Trust Architecture** the goal is...
Attack paths shrink once privileges, segments and management channels are consistently configured. For **Vulnerability Management & Patch Policy** the foundation remains the...
In network security, structure beats improvisation: clear paths, fewer privileges, and explicit trust boundaries. With **Backup & Disaster Recovery**...

Attack paths shrink once permissions, segments, and management channels are consistently configured. In **Logging, Monitoring & SIEM**, value emerges when...

In network security, structure beats improvisation: clear paths, fewer privileges, and explicit trust boundaries. For **Network Segmentation &...
In network security, structure beats improvisation: clear paths, fewer privileges, and explicit trust boundaries. With **MSSQL Hardening**, it's about...
Attack paths become small once privileges, segments and management channels are consistently configured. For **E-mail & DNS Hardening** the basis remains the same:...
In network security, structure wins over improvisation: clear paths, fewer privileges, and explicit trust boundaries. For **Windows Hardening**, the...
Attack paths shrink once permissions, segments, and management channels are consistently configured. For **Linux Hardening**, the foundation remains the same: less...
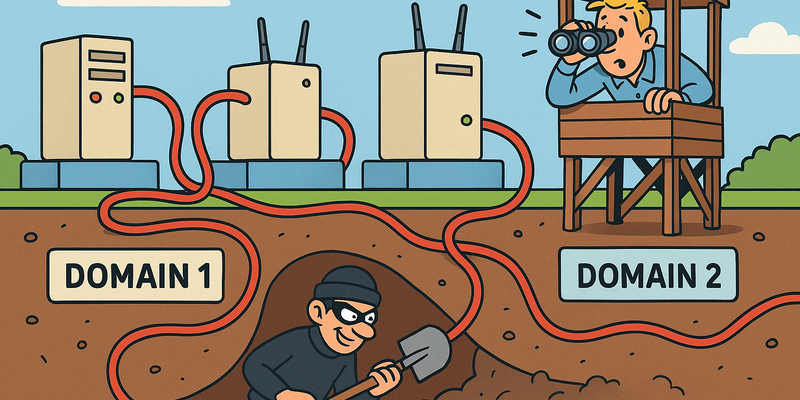
Attack paths shrink once privileges, segments, and management channels are consistently configured. For **Preventing Tunneling**, segmentation is the lever:...
Attack paths shrink once permissions, segments, and management channels are consistently configured. In **Detecting Persistence**, value emerges when...

In network security, structure beats improvisation: clear paths, fewer privileges, and explicit trust boundaries. For **ADCS Hardening**, privilege cleanup and...

Attack paths shrink once permissions, segments, and management channels are consistently configured. For **Credential Protection**, the foundation remains the same:...
Attack paths shrink once privileges, segments, and management channels are consistently configured. For **Stopping Lateral Movement**, segmentation is the lever:...
In network security, structure beats improvisation: clear paths, fewer privileges, and explicit trust boundaries. For **Kerberos Hardening**, privilege cleanup and...
In network security, structure beats improvisation: clear paths, fewer privileges, and explicit trust boundaries. With **Active Directory Hardening**...
In network security, structure beats improvisation: clear paths, fewer privileges, and explicit trust boundaries. For **Preventing Privilege Escalation**...
Attack paths shrink once permissions, segments, and management channels are consistently configured. In **Stopping Detection & Evasion**, value emerges when...
Attack paths shrink once privileges, segments, and management channels are consistently configured. For **Preventing Initial Access**, the basics remain the same:...
21 chapters on securing networks, Active Directory, Windows, Linux, and monitoring.
Klaar voor de volgende stap?
Een vrijblijvend gesprek van 30 minuten — geen sales, alleen technische sparring.